
Kingfisher
Open Source Secret Scanner with Live Validation
Detect, validate, and revoke leaked credentials across your codebase, Git history, cloud storage, and developer platforms. Built in Rust by MongoDB.
Why Kingfisher?
Scan Everything
Files, Git repos, GitHub, GitLab, Azure Repos, Bitbucket, Gitea, Hugging Face, Docker images, AWS S3, Google Cloud Storage, Jira, Confluence, Slack, and Microsoft Teams.
Live Validation
Automatically validate discovered credentials against provider APIs. Eliminate false positives by confirming which secrets are actually live and active.
Blast Radius Mapping
Go beyond detection. Map leaked keys to their effective cloud identities and exposed resources with --access-map. See exactly what an attacker could access.
Direct Revocation
Revoke compromised credentials directly from the CLI for 29 provider families including GitHub, GitLab, Slack, AWS, GCP, Heroku, and Cloudflare.
Open Source
Apache 2.0 licensed. Free to use, modify, and distribute. No vendor lock-in, no usage limits, no telemetry. Fully auditable codebase backed by MongoDB.
Built for Accuracy
Lightweight parser-based context verification across 16 supported languages reduces false positives at the detection layer. Combined with entropy filtering, checksum verification, and live validation, Kingfisher delivers high-signal results you can act on.
Built for AI
Detects and validates tokens for 35+ AI/ML providers including OpenAI, Anthropic, Google Gemini, Mistral, Cohere, and more. Purpose-built TOON output format for token-efficient LLM and agent workflows.
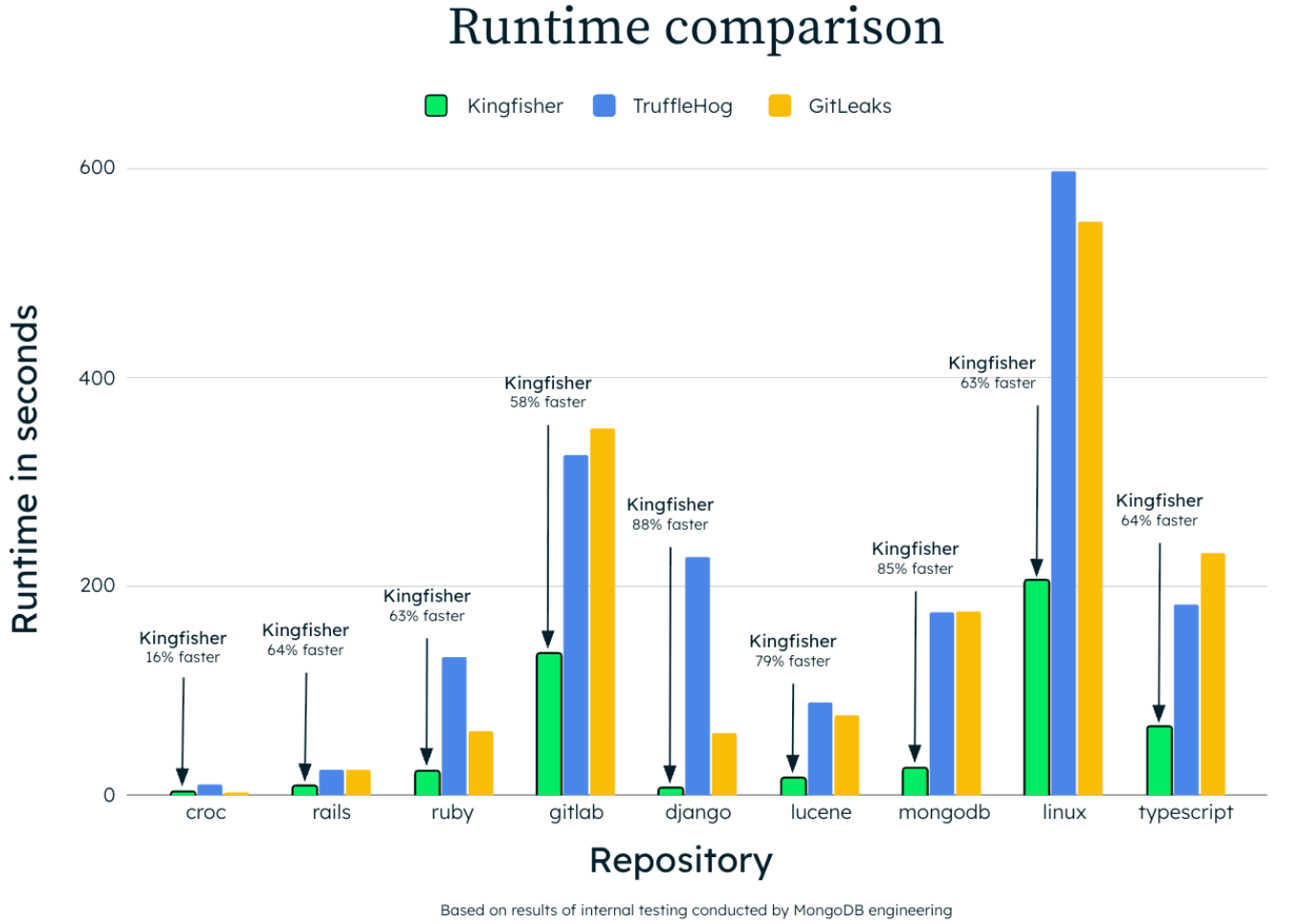
Built for Speed
Rust-powered with Intel Hyperscan SIMD-accelerated regex. Multithreaded scanning handles massive codebases while making minimal network requests through intelligent validation.
Performance
Kingfisher scans the Linux kernel in 205 seconds and the GitLab monorepo with just 17 HTTP validation requests. Intelligent validation means fewer API calls and faster results at scale.
Scan Targets
Install in Seconds
Homebrew
brew install kingfisherPyPI
uv tool install kingfisher-binDocker
docker run --rm -v "$PWD":/src ghcr.io/mongodb/kingfisher:latest scan /srcScript
curl -sSL https://raw.githubusercontent.com/mongodb/kingfisher/main/scripts/install-kingfisher.sh | bash